As a result, should your smartphone fall into the wrong hands, it is a potential treasure trove of information and, therefore, a potential cyber security risk.
If you download a rogue app, click on a malicious link in an email or visit a dubious website, it’s even possible for hackers to hijack your phone without it leaving your side.
Here are 10 smartphone security tips to help keep you and your device safe and secure.
1. Guard your smartphone and make use of security settings
Treat your phone as carefully as you would your bank cards. Take care when using your phone in public, and don’t let it out of your possession. Thieves can quickly rack up huge bills on stolen phones, and you may be liable for all charges run up on your phone before you have reported it lost or stolen to your provider. To help prevent this happening, protect your phone against unauthorised use by setting up a PIN, password or biometrics-based security for your lock screen via your devices settings.
2. Take precautions in case your phone is lost or stolen
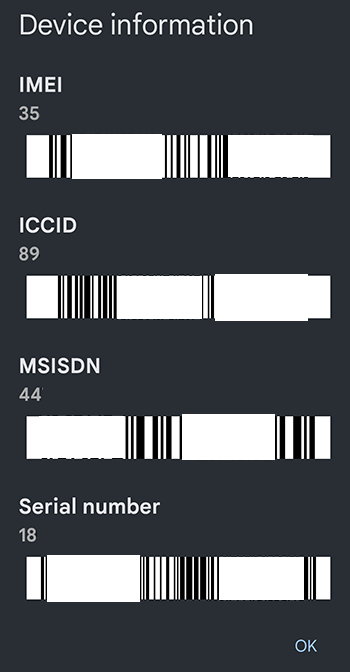 Make a record of your phone’s IMEI number, as well as the make and model number. The IMEI is a unique 15-digit serial number which you will need to give to your mobile operator to have your phone blocked. You can check your IMEI number by ‘dialling’ *#06# in your calls app (device information is displayed on-screen, rather than making an actual call). These details are also noted on a phone’s original packaging.
Make a record of your phone’s IMEI number, as well as the make and model number. The IMEI is a unique 15-digit serial number which you will need to give to your mobile operator to have your phone blocked. You can check your IMEI number by ‘dialling’ *#06# in your calls app (device information is displayed on-screen, rather than making an actual call). These details are also noted on a phone’s original packaging.
Consider making your phone less useful to potential thieves by barring calls to international numbers and premium rate lines, if you never use them. Some mobile insurance policies, or any other policies that may cover the phone, could provide limited cover for unauthorised use. It’s worth checking the terms and conditions of your existing policy, and when considering a new policy.
The national Mobile Phone Crime Unit’s Immobilise database is a free registration service that assists thepolice in reuniting owners with their stolen smartphones. For further details and contacts for different operators, see Ofcom’s Lost or Stolen Phone Guide.
3. Don’t override your smartphone’s security settings
It is not advisable to attempt to ‘crack’, ‘jailbreak’ or ‘root’ your smartphone or tablet. This is a process people use to remove restrictions placed on their device’s operating system by the phone manufacturer. Doing so carries considerable risks: it compromises the security of your device and may leave you more vulnerable to malicious software. It is also likely to invalidate your manufacturer’s warranty.
4. Back up and secure your data
Smartphones offer the option to back up your data to the cloud and/or a personal computer, so that you don’t lose data if your phone goes astray. Check for information on how to do this in the phone’s manual.
5. Install apps from trusted sources only
Apps are the easiest way for someone to hack into your phone. Sometimes hackers will take a popular paid-for app, add their own illegitimate elements and then offer it for free on ‘bulletin boards’, ‘peer-to-peer’ networks or through fake online stores. Once the rogue app has been downloaded to your phone, the hacker can potentially take control of the handset, incur charges via premium SMS without your permission, make calls, send and intercept SMS and voicemail messages, or browse and download online content. You may not be aware anything is wrong until it’s too late. Only download apps from official stores (e.g. App Store, Google Play), and exercise care – research the app and check reviews.
6. Use antivirus software
It’s not just rogue apps which pose a threat to your smartphone’s security. Viruses and spyware can also be downloaded from websites, or by connecting your device to an infected computer. Some phones may be more vulnerable than others, but you can check for antivirus software in a reputable app store. Also, before connecting your device to a computer, ensure it has the latest antivirus/antispyware and firewall installed and running.
7. Use software to find your phone or erase its data if it goes missing
This software is typically installed by default on most smartphones, allowing you to log in to a website or an app on another device to track your phone and take action. Examples include Apple’s Find My app and Google’s Find My Device for Android.
8. Clear your phone before you dispense with it
If you decide to donate, resell or recycle your smartphone, remember to erase any data on it first. Remove and erase any media cards and perform a full or ‘factory’ reset by going into the Settings menu.
9. Accept updates and patches
From time to time, you’ll be prompted on screen to update your operating system. App developers may also propose updates to their app. It is advisable to accept these updates as they become available. As well as typically offering new features and improving your phone’s performance, they can also fix security vulnerabilities.
10. Check if your smartphone security has been breached
 Additionally, there are some lesser-known tricks to check whether your smartphone is being tracked or if your security has been breached:
Additionally, there are some lesser-known tricks to check whether your smartphone is being tracked or if your security has been breached:
- Dial *#21# to see whether your data, including SMS, are being forwarded to a third party.
- Dial *#62# to see if your calls are being automatically forwarded. If so, where are your calls forwarded to? Don’t be too alarmed initially if you see that your calls are forwarded to a number you don’t recognise. This number might be a separate voicemail box run by your network service provider. The digest message might say that your calls are forwarded to this number after 20 seconds or so. Mobile service providers often provide separate voicemail gateways, including for those overseas on roaming charges. But you should certainly double-check with your service provider. Some suspicious numbers of known scammers and criminals are published online at unknownphone.com.
- Dial ##002# to stop your calls being automatically forwarded.
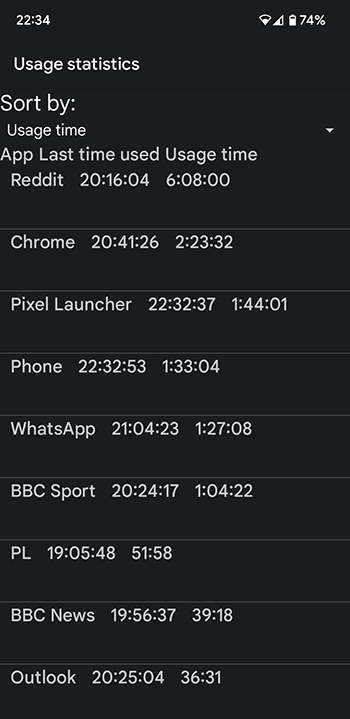
- Dial *#*#4636#*#* to find detailed configuration about your phone including call redirects, current network, usage and location. Check ‘Usage Statistics’ and ‘App Count Usage Time’ to double-check app usage and remove any apps that are suspicious (for example, you might not use them, but they show high usage).
Further smartphone security advice and support
For further advice on securing your smartphone and other digital device, or if you think your device has been compromised, contact us at advice@esarisk.com, on +44 (0)343 515 8686 or via our contact form. We’re here to support you.
You may also be interested in:
- The most common security threats to mobile devices
- How to know if you’ve been hacked and what to do about it.